LDAP authentication
As part of my BACHELOR Cybersecurity training, I would like to present this article on authentication and one of its methods:
The most challenging security issue associated with cloud computing is the management of individual identification and its related rights and permissions across individual information centers and public cloud websites.IDaaS providers keep cloud-based individual profiles that authenticate users and modify access resources or applications from safety terms, user groups, and personal privileges. The ability to combine with different directory companies(human directory, LDAP, etc…) and support is important. That’s why I choose to talk about LDAP.
LDAP «Lightweight Directory Access Protocol protocol» is an open, vendor-neutral, industry-standard application protocol for accessing and maintaining distributed directory information services over an Internet Protocol network. Directory services play an important role in developing intranet and Internet applications by allowing the sharing of information about users, systems, networks, services, and applications throughout the network. For example, a directory is a list of subscribers with an address and phone number.
LDAP is specified in a series of Internet Engineering Task Force StandardTrack publications called Request for comments, using the description language ASN.1. The latest specifications Version 3. So What can LDAP do?
LDAP allows access to data quietly, it guarantees password protection, identity verification, and backup of sensitive data, hackers cannot access the database using the LDAP protocol, which has a strong authentication method
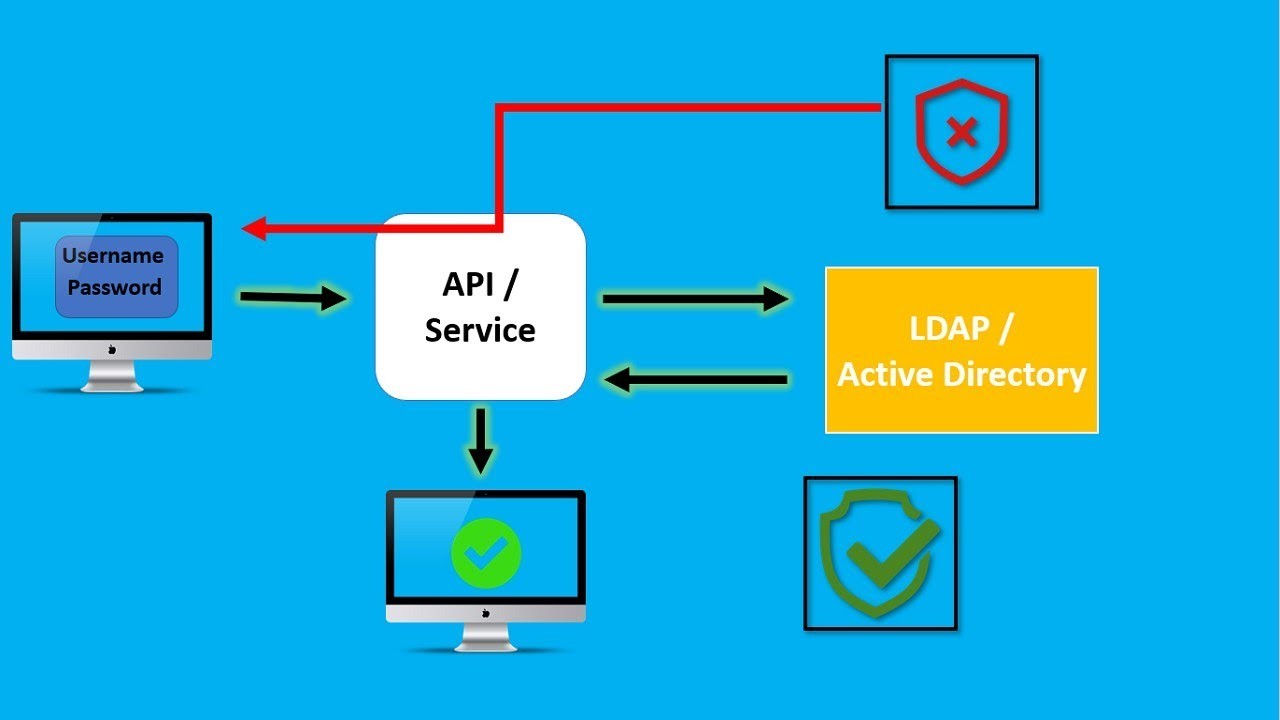
The query is only executed after the user is authenticated with the LDAP and it can be done using these two methods:
Recommended by LinkedIn
Is LDAP enough for a secure authentication or should we add something?
LDAP is a secure protocol, both in the implementation and in the authentication process. Additionally, it narrows the communication gap between Active Directory services and users, and it focuses on providing the maximum level of security by managing authentication with an access management layer. It then communicates the information to users. It allows them to understand the digital infrastructure and the database without compromising on security.
There are other security practices companies can consider improving directory security:
Conclusion :
As companies grow, they evolve in terms of complexity, particularly in terms of the needs related to their authentication system. This becomes a requirement in terms of safety and efficiency for employees. Single sign-on using LDAP is a very popular and widely used authentication mechanism today.



