Checksum - Error Detection Method
A checksum is a value derived from a dataset (like a file, message, or block of data) using a specific algorithm, designed to verify the integrity or authenticity of that data. Think of it as a digital fingerprint: it’s a compact representation of the data that can be used to detect errors, corruption, or tampering.
How Checksums Work
A checksum is generated by running the data through a mathematical function (often a hash function or a simpler algorithm). This function processes the data—bit by bit or in chunks—and produces a fixed-length output, typically a number or string. If even a single bit of the original data changes, the resulting checksum will differ, signaling that something’s off.
For example:
- You have a file: hello.txt with the content "Hello, world!"
- An algorithm (say, MD5 or a basic sum) processes it and outputs a checksum like 5d41402abc4b2a76b9719d911017c592.
- If someone edits the file to "Hello, world!!" and you recompute the checksum, it’ll be different (e.g., dffd6021bb2bd5b0af676290809ec3a5).
Common Uses of Checksums
1. Data Integrity Verification
- When downloading a file, a website might provide a checksum (e.g., SHA-256). You calculate the checksum of your downloaded file and compare it to the provided value. If they match, the file wasn’t corrupted during transfer.
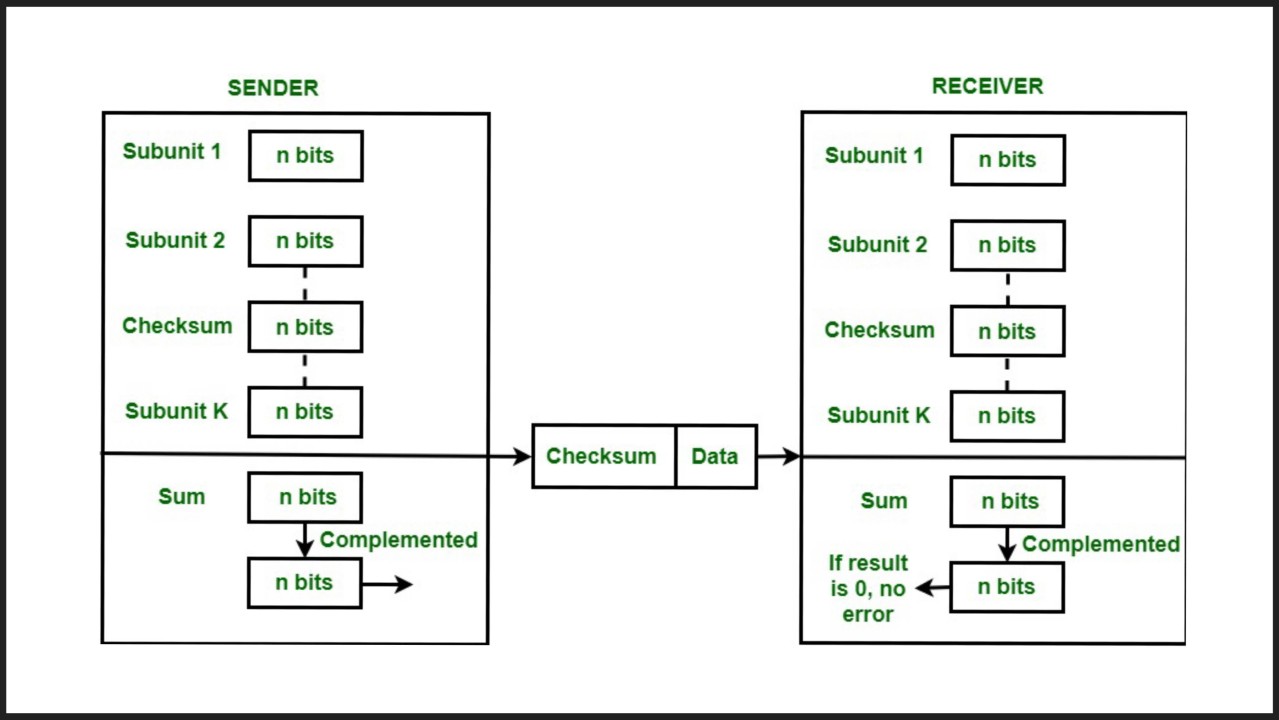
2. Error Detection
- In networking, checksums are used in protocols like TCP/IP to ensure packets aren’t garbled during transmission. If the receiver’s checksum doesn’t match the sender’s, the packet is discarded or retransmitted.
3. Tampering Detection
- Software distributors use checksums to prove their files haven’t been altered by malicious actors. A mismatched checksum could indicate a hacked file.
4. Database and File Systems
- Checksums help detect corruption in stored data, ensuring backups or records remain intact.
Types of Checksum Algorithms
- Simple Checksums
- Example: Adding up all the bytes in a file and taking the result modulo some number (e.g., 256). Fast but not very reliable for detecting subtle changes.
- Cyclic Redundancy Check (CRC)
- Example: CRC32. More sophisticated, using polynomial division to catch common errors like bit flips. Widely used in hardware and file formats (e.g., ZIP files).
- Cryptographic Hash Functions
- Examples: MD5, SHA-1, SHA-256. These produce longer, more unique outputs and are harder to reverse-engineer or fake. They’re common in security contexts but can be overkill for basic error checking.
Strengths and Weaknesses
- Strengths : Quick to compute, effective for catching accidental errors, and widely supported.
- Weaknesses : Simple checksums can miss complex errors (e.g., two changes canceling out). Cryptographic hashes are stronger but slower and still vulnerable to collisions (two different inputs producing the same output) in rare cases.
Recommended by LinkedIn
Example
In short, a checksum is a handy tool for ensuring data stays true to its original form, whether you’re downloading files, sending network packets, or managing database migrations. Let me know if you want a deeper dive into any specific aspect!
Benefits of Checksums in Databases
1. Ensures Data Isn’t Corrupted
- Saves a checksum with the data. If it matches later, the data’s safe.
- Example: Prevents a $100 transaction from turning into $10 due to a glitch.
2. Spots Changes Quickly
- Compare checksums instead of entire datasets to see what’s different.
- Example: Syncs only changed articles in a blog system, saving time.
3. Detects Tampering
- A mismatched checksum flags unauthorized edits.
- Example: Shows if a hacker changed a user’s role in a database.
4. Verifies Backups
- Matching checksums confirm backups and restores are correct.
- Example: Ensures customer data restores properly after a crash.
5. Resolves Conflicts
- In multi-server setups, checksums highlight data mismatches.
- Example: Catches inventory differences across warehouses.
6. Boosts Performance
- Comparing small checksums is faster than full data checks.
- Example: Speeds up caching in busy apps.
7. Validates Migrations (e.g., Prisma)
- Ensures migrations don’t mess up data.
- Example: Prisma uses checksums to check migration files; you can use them for data too.
Downsides
- Weak checksums might miss rare issues.
- Adds minor storage/processing cost.
- Detects problems but doesn’t fix them.